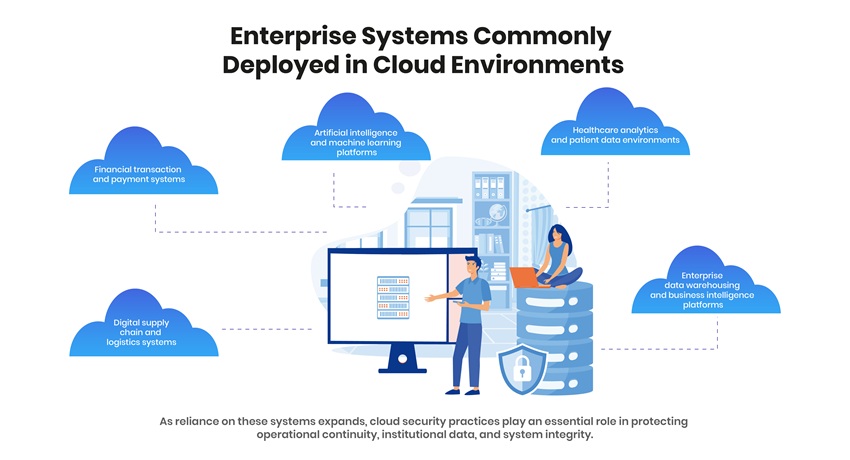
Cloud computing has become central to the operation of modern digital systems. Artificial intelligence applications, financial platforms, healthcare analytics environments, and enterprise data systems are increasingly deployed and managed within distributed cloud architectures.
World Cloud Security Day 2026 provides an opportunity to examine how organizations are approaching the protection of cloud-based infrastructure and data systems. As enterprises expand the use of multi-cloud environments, SaaS ecosystems, and distributed computing frameworks, the scope and complexity of security responsibilities have also increased.
Cloud platforms allow organizations to scale services, deploy analytics capabilities, and integrate digital systems across geographic and operational boundaries. At the same time, these environments require consistent governance, visibility across infrastructure layers, and disciplined management of identities, configurations, and application interfaces.
In this context, cloud security has become a structural component of digital resilience.
Cloud Security and the Infrastructure Supporting Digital Systems
Cloud infrastructure now supports a large proportion of enterprise and institutional digital operations. Organizations rely on cloud platforms to manage large-scale data environments, deploy machine learning workloads, and operate globally distributed digital services.
Most enterprises now operate multi-cloud or hybrid cloud architectures, integrating infrastructure services, SaaS platforms, and application environments across multiple providers.
Cloud Security in Expanding Multi-Cloud Ecosystems
Modern enterprise cloud environments differ significantly from traditional centralized IT infrastructure. Cloud architectures connect infrastructure services, application environments, APIs, identity platforms, and third-party integrations within distributed operational networks.
Each additional application, user identity, or integration increases the number of access pathways that must be governed and monitored.
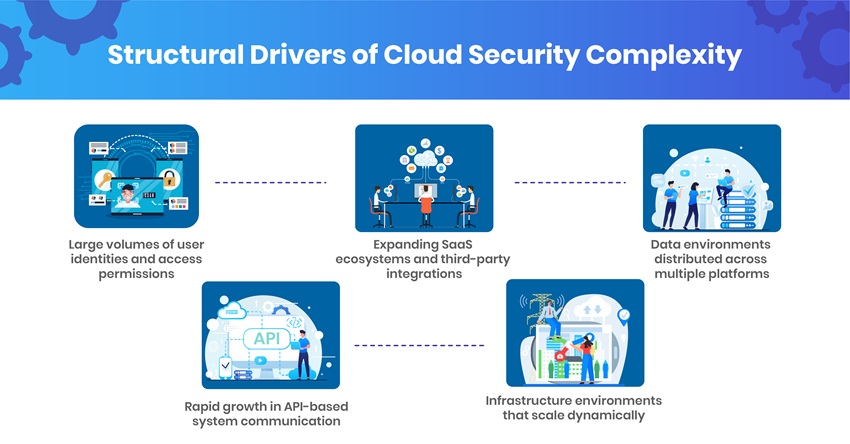
For security teams, maintaining consistent visibility, policy enforcement, and access governance across these distributed systems has become a central operational responsibility.
Cloud Security Considerations in the Context of AI-Enabled Threat Activity
Advances in artificial intelligence are influencing both cybersecurity defense capabilities and cyber attack techniques. Machine learning tools allow threat actors to analyze infrastructure behavior, test system responses, and automate certain stages of attack development.
These developments increase the speed at which vulnerabilities can be identified and exploited.

To address these developments, many organizations are deploying security analytics platforms that incorporate machine learning to identify anomalous activity and support faster incident response.
Cloud Security Risks Associated with Misconfiguration and API Exposure
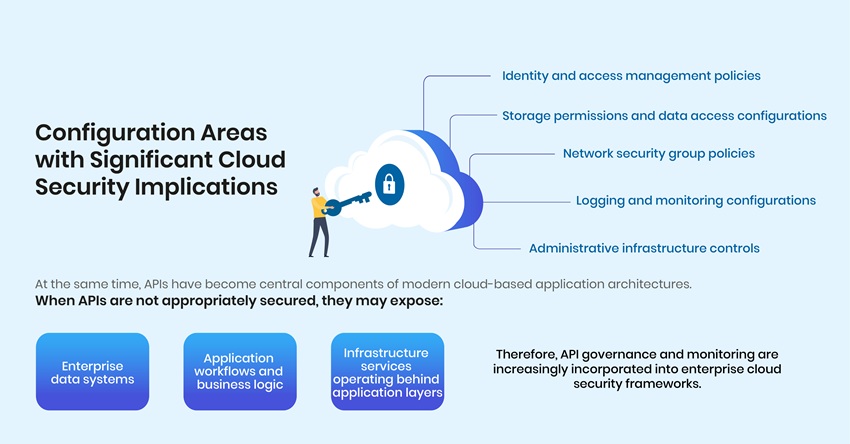
A significant proportion of cloud security incidents continue to originate from configuration errors. Cloud environments provide extensive flexibility in how infrastructure, data access, and identity permissions are configured. This flexibility requires disciplined governance and consistent configuration oversight.
A single configuration error can create unintended access to data or administrative controls.
The Analytical Dimension of Cloud Security
Cloud systems generate large volumes of operational and security-related telemetry. Network activity, system logs, application events, and user behavior data provide signals that can indicate system anomalies or emerging threats.
Interpreting these signals requires analytical techniques capable of identifying patterns across large data environments.
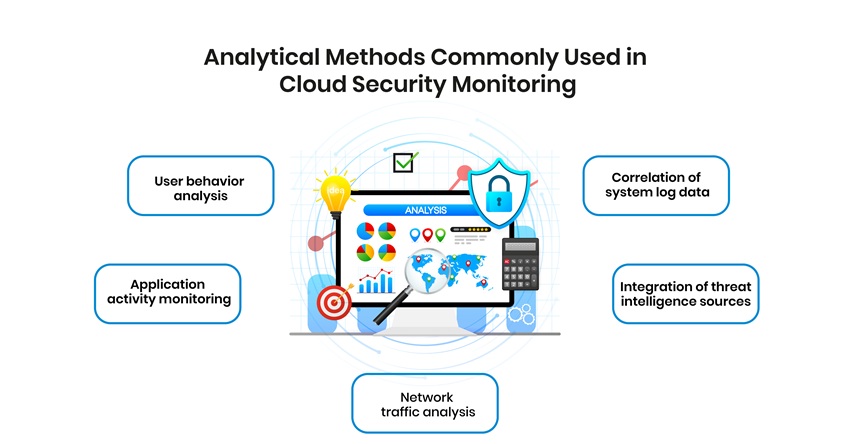
These analytical approaches increasingly combine cybersecurity expertise with data science capabilities to support early detection of abnormal system activity.
Conclusion
Cloud infrastructure now supports many of the systems that underpin contemporary digital economies. As organizations continue to expand the use of distributed cloud architectures, the responsibilities associated with protecting these environments will continue to grow.
Effective cloud security requires governance frameworks that integrate infrastructure management, identity control, secure application design, and continuous monitoring of system activity.
Organizations that develop structured approaches to cloud security will be better positioned to protect operational systems, safeguard institutional data, and maintain confidence in digital services.
Frequently Asked Questions
What is World Cloud Security Day and why is it important?
World Cloud Security Day, observed on April 3, is a global awareness initiative focused on protecting data and applications in cloud environments. It highlights risks such as misconfigurations, identity-based attacks, and unsecured cloud usage, emphasizing the need for stronger security practices and governance across distributed systems.
Why is cloud security more complex in multi-cloud environments?
Multi-cloud environments involve multiple platforms, APIs, and integrations, which increase access points and require consistent governance, visibility, and security policy enforcement across systems.
What are the most common causes of cloud security breaches?
Misconfigurations, weak identity and access management (IAM) policies, unsecured APIs, and inadequate monitoring are among the leading causes of cloud security incidents.
How are AI technologies impacting cloud security threats?
AI enables threat actors to automate reconnaissance, identify vulnerabilities faster, and adapt attacks dynamically, increasing the speed and sophistication of cyber threats.
What role does data analytics play in cloud security?
Data analytics helps organizations monitor system activity, detect anomalies, and respond to threats by analyzing logs, user behavior, network traffic, and integrating threat intelligence.